
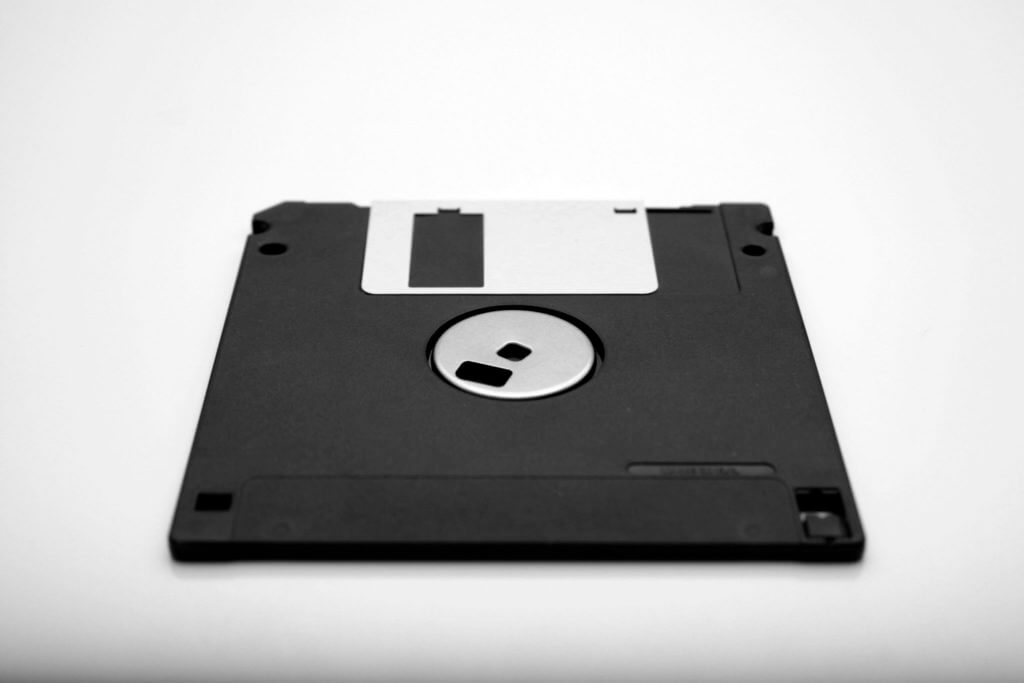
What Are the Real Risks of Aging Technology?
It’s very easy to spot outdated technology, at least. That’s what […]
What Are the Real Risks of Aging Technology? Read More »

It’s very easy to spot outdated technology, at least. That’s what […]
What Are the Real Risks of Aging Technology? Read More »

So Windows 10 has reached end of life. For many businesses
Is Windows 10 End of Life a Security Risk for Your Business? Read More »

Running your payment systems on outdated security protocols is like locking
Phishing Attacks: What Your Business Needs to Know to Stay Protected
What You Need to Know About Phishing Read More »
A well-managed, efficient, and skilled IT department is critical for YOUR
Is Your Company Suffering from Poor IT Workforce Management? Read More »
Understanding the 2025 Overtime Law Changes and Their Impact on IT
New Overtime Laws make IT Workforce Management Crucial Read More »
Why Network Monitoring Is Your Safety Net The Morning Surprise: When
Network Monitoring Can Keep Your Employees Working Read More »
Why You Need a Disaster Recovery Plan If your IT operation
Disaster Recovery Planning Read More »
A Disaster Recovery Plan? Does your business have a computer system
Do You Have a Disaster Recovery Plan? Read More »
Disaster Recovery: Plan Ahead, Stay Ready Disaster recovery is not a matter
Disaster Recovery – Be Prepared Read More »
What Comes to Mind When We Think About Disasters? When we
Disaster Recovery: Planning Ahead Read More »

Working With a Cybersecurity Professional Cybersecurity is probably the most important
Working with a Cybersecurity Professional Read More »
Mastering Keyboard Shortcuts for Efficiency Keyboard shortcuts are a series of
23 time-saving keyboard shortcuts Read More »
10 quick ways to speed up your computer Whether you’re on
10 quick ways to speed up your computer Read More »
10 horrible things that can happen to your business if you
10 horrible things that can happen to your business Read More »
Increase Network Security in Your Workplace You do as much as
4 Ways to Increase Network Security in Your Workplace Read More »
Security alert petya ransomware attack If you are on our maintenance
Security Alert: Petya Ransomware Attack Read More »
Understanding the Threat of Ransomware Health Data Management recently reported on
Disaster Recovery Issue: How Far Apart Are Your Backups? Read More »
Charleston’s Power Breakfast: A Timely Conversation on Health Care This past
Charleston Regional Power Breakfast Read More »
Your Go-To Guide for Cloud Services and Container Management Rather than
Cloud Services for Your Business – Container Hosting and Management Read More »
Why Security Testing Matters Organizations increasingly invest in security testing to
IT Security Services: Testing Your Cyber Security Defenses Read More »
Are You Sure Your Systems Haven’t Been Breached? You might say
Never Been Hacked? Are You Sure? Read More »
Employee Education and Network Monitoring At Kotori Technologies, we’ve spent over
Training and Monitoring: Best Defense Against Social Engineering Read More »
The Rise of Virtual Infrastructure in the Workplace Virtual infrastructure is
How Can Virtual Infrastructure Improve Your Business Model Read More »
Why Disaster Recovery Matters More Than Ever Disaster recovery is always
Take Disaster Recovery Seriously to Avoid Downtime from Hurricanes Read More »
Top 5 Security Tips for Protecting Your Business Network 1. Back
Smart IT Security Tips Read More »
For Faster Disaster Recovery There never is and never will be
Plan Ahead For Faster Disaster Recovery Read More »
Network Security Tips For Small Businesses Every modern business has a
Network Security Tips Read More »
Network Security Issues You Didn’t Know You Had Network Security is often
Network Security Issues You Didn’t Know You Had Read More »
Smart Devices, Real Threats: Why Cybersecurity Matters More Than Ever
Network Security Alert: Smart Devices real Threats Read More »
Play Video Q: What are the essential IT roles needed in
What are the 5 it roles needed in your business? Read More »

Creating a Successful Routine Remote work continues to be a reality
Creating a successful routine Read More »

Things They Don’t Tell You About Cybersecurity You can have every
5 things they don’t tell you about cybersecurity Read More »
Cultivating a Proactive Approach No business is safe from IT difficulties.
IT Workforce Management: Cultivating a Proactive Approach Read More »
IT Consulting Brings the Real World to Your Business to Help
IT Consulting Brings the Real World to Your Business to Help in Scale-ability Read More »
How Managed services can help your start-up Grow It is difficult
How Managed Services Can Help Your Startup Grow Read More »
WHY EVERY BUSINESS NEEDS MODERN IT SUPPORT Every business today needs
How IT Consulting Will Benefit Your Business Read More »
THE EVOLUTION OF BUSINESS DEPARTMENTS For decades, businesses worldwide operated with
Having a Hard Time with IT Workforce Management and Hiring? Here's Why Read More »
PLANNING FOR A SUCCESSFUL BYOD IMPLEMENTATION You’ve probably heard a lot
Get Help With Your BYOD Initiative Read More »
Four Things Network Monitoring Can Save If your company has ever
Four Things Network Monitoring Can Save Read More »
How IT Consulting Powers Smarter Business Decisions For many businesses, technology
Four Components of Effective IT Consulting Services Read More »
3 Ways Disaster Recovery Can Save your Business in Times of
3 Ways Disaster Recovery Can Save your Business in Times of Need Read More »
Security Threats That Can Impact Your Business Massive data breaches and
3 Network Security Threats That Can Impact Your Business Read More »
Can Your IT Configuration Withstand a Cyber-Attack? Many businesses underestimate how
Why you need high-quality IT security services for your audit Read More »
What is a (MSP) Q: What is a Managed Service Provider (MSP),
What is a Managed Service Provider (MSP) Read More »
Is It Time to Rethink Your Servers? The Hidden Costs of
Cloud Services Offer You Much Needed Flexibility Read More »
Kotori Technologies: Over a Decade in the Cloud Back in 2011,
Kotori Is In the Cloud Read More »
Doing My Part for the Planet Let me just say before
Blackle the Green Google… WHAT? Read More »
Q: What is a business continuity plan and why is it
10 reasons why you need a business continuity plan Read More »

Introduction to Google Business Introduction Hey guys welcome to the week
Intro to Google Business Read More »

Cybersecurity for Healthcare: Protecting Data, Patients, and Trust In today’s digital
Healthcare Cybersecurity: Understanding Confidentiality, Integrity, and Availability Read More »
Understanding Cybersecurity in Healthcare Healthcare organizations face special challenges in today’s
Managed It in Healthcare Read More »

The High Risk of Cyberattacks Healthcare businesses are easy targets for
Why Healthcare Businesses Need Strong Cybersecurity Read More »

Kotori Technologies Expands Team Kotori Technologies Expands Team with Heather Hill
Kotori Technologies Expands Team with Heather Hill to Support Growth in The Triad Region Read More »
The Benefits of Managed IT Services for Small and Medium Businesses
The Benefits Of Managed IT Services For Small and Medium Businesses Read More »

IT Challenges Facing Small Businesses Small businesses in the Triad region—encompassing
Top 5 IT Challenges Facing Small Businesses in the Triad Market (And How to Solve Them) Read More »

How Secure Are Your Systems? Why Testing Matters You might think
Penetration Tests Can Uncover Weaknesses Read More »
How to Handle a Business Data Breach: A Step-by-Step Guide Data
Handling a Business Data Breach Read More »

kotori Technologies Spotlight: Neadom Tucker Sometimes your technology just needs to
Kotori Spotlight: Neadom Tucker Read More »
Understanding Malware: What It Is, How It Spreads, and How to
What You Need to Know About Malware Read More »

This month we’re sharing Elizabeth’s story. Elizabeth Goodman was recently elected
Employee Spotlight: Elizabeth Goodman Read More »
When should you replace your work computer? Your company runs on
When should you replace your work computer? Read More »
Servant Leadership in a Remote World: Staying Connected from Afar There
Checking in: Servant leadership in a remote age Read More »
Managing The Remote Organization Many of us have been facing the
Managing the remote organization Read More »

Protecting Yourself From crisis Phishing scams There is a lot of
How to protect yourself from crisis phishing scams Read More »

Remote Meeting Etiquette: Do’s and Don’ts for Virtual Success A lot
Do’s and don’ts of remote meetings Read More »
How to Avoid Disaster Recovery Mistakes The vast majority of companies
How to avoid these 4 disaster recovery mistakes Read More »

Things They Dont Tell You About Outlook Email client Microsoft Outlook
5 things you didn’t know about Outlook Read More »
The rising threat of cyberattacks Cyberattacks are on the rise, and
You’ve been struck by ransomware. What’s next? Read More »

Play Video On-Premise vs. Hosted VoIP: What’s the Difference? Introduction Hey
Hosted VoIP vs on-premise VoIP Read More »
Play Video Are You an Easy Target for Hackers? Take Our
Are you an easy target? Read More »
Play Video Introduction Hey guys, this week on When You Need Them
9 hacks for presentation day Read More »
Microsoft Teams: The Ultimate Collaboration Tool Introduction Okay guys, check this
Meet Microsoft Teams Read More »
Play Video Browser Password Managers: Convenient but Cautious Hey guys, this
Browser password managers Read More »
Play Video Staying Connected When Disaster Strikes: A Business Continuity Guide
How to stay connected on the go Read More »
When You Need Em Ask Neadom: CRM for Your Business Hey
CRM for your business Read More »

the importance of pen testing Here is the importance of PEN
How PEN testing can save your company thousands Read More »

Virtual Kidnapping Virtual kidnapping is nothing new, but in an increasingly digital
What is virtual kidnapping? Read More »
Introduction: Password Best Practices Hey guys, I’m Neadom Tucker, and if
Password best practices Read More »
Spam Is on the Menu: How to Keep Your Inbox Clean
How to stop spam emails Read More »
Five Marketing Mistakes Business Owners Make Introduction Hey guys, welcome to
5 Marketing Mistakes Business Owners make Read More »
How to Tell Your Boss Your Computer Sucks (Without Getting Fired)
How do I tell my boss my computer sucks? Read More »
Ask Neadom Hey guys, this week on “When You Need ‘Em,
AI for your business Read More »
Microsoft Edge vs Internet Explorer: What You Need to Know Introduction
Internet Explorer vs Microsoft Edge Read More »
5 Office 365 Tips to Customize and Boost Productivity Introduction What’s
5 life changing Office 365 hacks Read More »
Ask Neadom: The Perfect IT Recipe (Spaghetti and Meatballs Edition) Introduction
The perfect IT recipe Read More »
OPENING REMARKS Hey guys, today on “Ask Neadom”, I’m gonna play
Why updates matter Read More »

Ask Neadom: 5 Reasons Your Computer Is Running Slow Introduction Hey
5 reasons your computer is slow Read More »

Marie Kondo Your Business: Declutter Your Tech, Team, and Time Introduction
How to Marie Kondo your business Read More »

Is Facebook Safe Anymore? Introduction What’s going on everybody? This is
Is Facebook still safe? Read More »

Cloud Security Explained: Protecting Your Data Like Your Front Door Introduction
How secure is the cloud? Read More »

Budgeting for Business Computers and Laptops Introduction What’s going on everybody?
How much should you spend on a computer? Read More »

How Much Security Is Enough? 5 Essentials Every Small Business Needs
How much should I spend on cybersecurity? Read More »

Avoiding IT Nightmares: How the Right Partner Protects Your Business Introduction
Your prescription for a healthy business Read More »
To be Exploring the Dark Web: What It Is and How
What is the dark web? Read More »

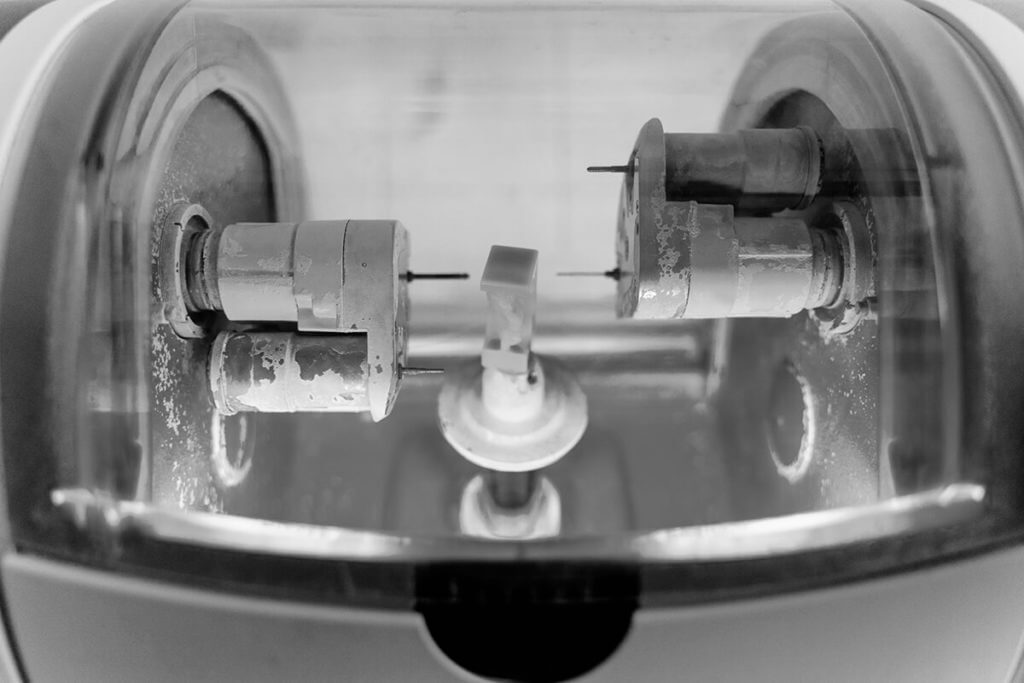
Ask Neadom: Inside the Sophos XG 750 Firewall – Unboxing and
Sophos XG 750 firewall unboxing and installation of FlexiPort module Read More »

What Does “End of Life” Mean for Your Business? By Neadom
What is end of life? Read More »

What information and vulnerable data might your employees be telling hackers? Reach out to Kotori today to learn more.
4 things your employee is telling your hacker Read More »
want better it? Solutions? Be like the characters from friends “Friends”
Want better IT? solutions? Be Like the characters from ‘Friends’ Read More »
What’s the secret for better cybersecurity? TRAINING. What, you want to
One simple secret for boosting employee cybersecurity awareness Read More »
3 reasons most CEOs don’t understand technology and how to overcome
3 reasons most CEOs don’t understand technology and how to overcome it Read More »
Ask Neadom: Unboxing and Review of the Sophos XG 230 Firewall
Sophos XG 230 Firewall unboxing Read More »

Why Business Owners Should Avoid Buying Computers from Big-Box Retailers Introduction
3 reasons not to buy a business PC retail Read More »
We were talking to your Mom last night, but then again
5 ways your mama lied to you about network security Read More »
The Art of Cyber Defense: Strategy Lessons from Sun Tzu Thousands
Sun Tzu on the art of cybersecurity Read More »

Ask Neadom Introduction Hey guys, today on Ask Neadom, we’re taking a
What’s on Neadom’s desktop? Read More »
Learn About Your Computer From Fortnite Fortnite is the critically-acclaimed shooter
3 things you can learn about your computer from Fortnite Read More »

Ask Neadom: Mac vs. PC – The Tech Super Bowl Showdown
Tech Bowl MAc VS PC Read More »

When You Need Him: Ask Neadom – Your Computer Needs a
Get your computer on a diet Read More »
Don’t Get Hooked: Protect Your Business from Phishing Attacks Hearing the
Phishing scams: Don’t open that email! Read More »
Understanding Single Sign-On (SSO) and Its Impact on Your Business Introduction
What is single sign on? Read More »

serious IT compliance mistakes you’re making right now There are plenty
7 serious IT compliance mistakes you’re making right now Read More »

What Does Your IT expert want you to leave in 2018
5 things IT experts want you to leave in 2018 Read More »

Introduction: should I get managed services Hey guys, today on When You
Should you get managed services? Read More »

Security Starts with You: Building Habits That Protect Your Network You
The biggest risk to cybersecurity: you! Read More »

Why Wired Networks Still Matter in a Wireless World Hey guys!
Wireless everything?! Read More »

Why Training should be your first step to cyber security These
Why training should be your first step to cybersecurity Read More »
Four Essential IT Tips for Your Business in 2019 Welcome to
How to prepare your business for the New Year Read More »
Cheat sheet on Disaster Recovery You hope that you never have
The ultimate disaster recovery cheat sheet: Part 3 Read More »

Internet Service Provider Summary and Final Thoughts
Internet service providers summary Read More »
The ultimate disaster recovery cheat sheet: Part 2 Disaster Recovery 101:
The ultimate disaster recovery cheat sheet: Part 2 Read More »
Understanding Internet Speeds for Your Business From the series: When You
Which internet speed should you choose? Read More »
Disaster Recovery 101: Employees & Operating Your Business When disaster strikes,
The ultimate disaster recovery cheat sheet: Part 1 Read More »
Introduction: Internet Service Provider Hey guys, on this week of When You
Which internet service provider should I choose? Read More »
common myths about disaster recovery If you are a small business
5 common myths about disaster recovery Read More »

Password Mistakes That Put IT Companies At Risk Passwords are like
7 password mistakes putting IT companies at risk Read More »

Understanding MSP Managed Services: Software and Licensing Introduction This week on Ask
Managed services software & licensing Read More »

Growing Reliance on IT Systems As your business or organization grows,
Is your managed services provider leading you to success? Read More »

Ask Needham: How Much Antivirus Do You Really Need? Introduction Hey
Can you have too much antivirus? Read More »

Managed services Welcome back everyone to When You Need em ask, Neadom.
What is the cost of managed services? Read More »

Kotori Technologies Expands Charleston, SC – November 08, 2018 – Kotori Technologies,
Kotori Technologies moves to a new location Read More »
How deep does your disaster recovery plan go? Disaster recovery is
The dangers of an incomplete disaster recovery plan Read More »
Play Video Introduction: Managed services Hey guys, thanks for joining us
What are managed services? Read More »

North Charleston, SC – October 31, 2018 The North Charleston Rotary
Elizabeth Goodman of Kotori Technologies, LLC receives Rosser Thrash Award Read More »

When you Need em ask Neadom: retail PC Welcome to “When
Why you shouldn’t buy your business PC from a retail store Read More »

Manufacturing in the Digital Age: What You Need to Know About
Industry 4.0: Trends To Look Out For Read More »
Sophos Accreditation Empowers Kotori Technologies to Deliver Smarter IT Security
Kotori Technologies, LLC Achieves Synchronized Security Accreditation Read More »

That’s what penetration testing tells you. Firstly, there’s a lot of
Here’s How We Would Steal Your Company’s Data Read More »

BYOD Without a Policy? Think Again. BYOD, don’t bring your own
BYOD: Don't Bring Your Own Device Until You Bring in a Policy Read More »

Why Managed IT Support Is the Smart Way to Prevent Business
Why Is Managed IT as a Service a Better Investment than Traditional IT Support? Read More »
2 Unpopular Essentials for Computer Security Two unpopular essentials for computer
2 Unpopular Essentials for Computer Security Read More »
Don’t Let Digital Clutter Ruin Your Summer: Essential Network Cleanup Tips
Two Summer Maintenance Essentials for Your Company's Computers Read More »
Simplify Your Data Responsibilities and Strengthen Security with Smart IT Solutions
What Kind of Data Is Your Business Storing? Read More »
IT is improving Manufacturing The manufacturing industry has served as a
How IT is Improving Manufacturing Read More »

Network Monitoring Attacks on the Internet are a fact of life.
Network Monitoring for Security Read More »

How BYOD Policies Can Expose Your Business to Cybersecurity Risks Any
Your Employees’ Personal Devices Invite Man-in-the-Middle Attacks Read More »
Why Your Business Should Switch to VoIP: Smarter, Flexible, and More
3 reasons you need VoIP Read More »
Stop Wrestling with Tech: Partnering for Smarter IT Solutions If you
IT Workforce Management: Escape The Maze Read More »

Operational Costs and Managed IT Services Operational costs can stretch a
Use Managed Services to Balance Your Business Budget Read More »
Server with Cloud Services It’s the end of audit season, and
Replace Your Next Server with Cloud Services Read More »
Myths About IT Responsibilities Working in IT isn’t easy. There’s always
6 Myths about IT Responsibilities Read More »
Every minute data records are lost or stolen. Every minute, 3,270 data
10 Questions to Test Your Employee's Cybersecurity Awareness Read More »
Cloud services for small to meduim sized businesses can optimize productivity
Cloud Services For Small and Medium Sized Businesses Can Optimize Productivity Read More »
Think Before You Toss When you’re done with business documents, your
Business Security and Paper Shredding Read More »

The Power and Peril of Mobile Device Flexibility Mobile device technology
Reap the Benefits of BYOD (Bring Your Own Device) Without the Risks Read More »

CHANGE MANAGEMENT HELPS OPTIMIZE BUSINESS OPERATIONS There’s an old saying: “The
3 Principles of Change Management to Help Optimize Business Operations Read More »

What Are Host-Based Firewalls? Firewalls are often seen as network appliances
Use Host Based Firewalls to Boost Your Organization's System and Network Security Read More »

Bring Your Own Device Security Issues Although BYOD enables real-time mobile
BYOD: Bring Your Own Device Security Issues Read More »
The Shift to Virtual Infrastructure More and more companies are realizing
Virtual Infrastructure Considerations Read More »

Kotori Technologies Partners with Elms Digestive for IT Services New Partnership
Kotori Technologies Contracts with Elms Digestive for IT Needs Read More »

Be Ready Before the Full Story Breaks Cyber threats often catch
With Managed IT as a Service, Respond Quickly to Cyber Threats Read More »
Smart Change Management for Smarter Manufacturing To successfully rely on their
Change Management for Manufacturing Companies: Four Considerations Read More »
Is the Cloud Right for Your Business? The Cloud Is Changing
Sometimes Network Monitoring is Still the Right Decision Read More »

Why IT Consulting Makes Sense for Your Business With the state
Can Your Business Use The Services Of An IT Consulting Firm? Yes! Read More »
The Shift in Business Communication Communications is important for all businesses.
Are You Ready To Implement VoIP Phone Systems Into Your Workplace? Read More »

Why You Need a Disaster Recovery Plan If you haven’t prioritized
What Will You Do If Ransomware Strikes? Read More »
Manufacturing Organizations Finding Good Tech Help If you’re like most business
How Manufacturing Organizations Find Good Tech Help Read More »

Productivity and BYOD policy The BYOD policy is an important part
Productivity and BYOD Policy, A Necessity Worth the “Risk” Read More »
Supporting Your Technology Department Managing a technology department can feel daunting,
Change Management Is Simple Read More »
When the Plan Falls Apart Remember that time you had a
Network Monitoring Makes Your Business More Efficient Read More »
Backup vs. Recovery: Why Planning Ahead Prevents Data Disasters You’ve returned
Your Servers Crashed- Now What? Read More »
5 Simple Reasons You’ll Want to Consider an IT Consult Your
5 Simple Reasons You'll Want to Consider an IT Consult Read More »
7 Reasons Why You Should Care About BYOD Policies BYOD ,
7 Reasons Why You Should Care About BYOD Policies Read More »
Are You Part of the Trend? Cloud services usage continues to
Increased Use of Cloud Services: Are You Part of the Trend? Read More »
Digital Transformation in Manufacturing Your manufacturing floor just shut down. Your
Manufacturing in the Digital Age Read More »
Help Improve Your Email Use Emails are a fundamental form of
IT Consulting Can Help Improve Your Email Use Read More »
BYOD: A Smart Move for Productivity and Cost-Savings Bring Your Own
The Good and Bad Regarding BYOD Read More »
IT Workforce Management Helps Prevent Chaos A recent slideshow posted to
Strong IT Workforce Management Helps Prevent Chaos Read More »
Fiber Optic Network Need Protection Too Cable cords are becoming a
Don't Forget Your Network Security: Fiber Optic Networks Need Protection Too Read More »
Bridging the Gap: How IT Workforce Management Enhances Communication and Business
How Can IT Workforce Management Cut Down on Poor Communication? Read More »
It’s 2 AM. Do you know whether your website is running
Network Monitoring Needs to Be 24/7 Read More »
Why Every Business Already Has a BYOD Policy. Even If You
Why Your Company Needs A Formal BYOD Policy Right Now Read More »
Computer Security Isn’t Easy Computer security isn’t easy, and if your
IT Security Services Can Save Your Business Read More »
IT Change Management Adopting broad changes to your IT infrastructure presents
IT Change Management: Are You Communicating Clearly? Read More »
Internet Threats to Businesses The internet is a dangerous place for
8 Top Internet Threats to Businesses Read More »
Do You Have the Right IT Team? When it comes to
IT Consulting Advice: Is It Time For You To Make The Switch? Read More »
How Is Virtual Infrastructure Bigger Inside Than Out? Virtual Infrastructure for
How Is Virtual Infrastructure Bigger Inside Than Out? Read More »
IT Change Management Solutions Bring Benefits To Your Business Professional change
IT Change Management Solutions Bring Benefits To Your Business Read More »
Issues IT Consulting Can Uncover CEOs and business owners need to
Three Key Issues IT Consulting Experts Can Uncover Read More »
Getting the Most from Managed Services Starts with Communication A recent
Communication is Key to Getting the Most Out of Managed Services Read More »
The Dangers of Hacking and Impersonation A disturbing story came out
IT Consulting Experts Warn About Impersonation Read More »

Bring Your Own Device BYOD (Bring Your Own Device) is a subject
Potential Legal Liabilities with BYOD Read More »
IT Solutions for the Manufacturing Industry Automation and the Need for
Manufacturing IT Solutions by Kotori Technologies, LLC Read More »
Recovering from Disaster, the easy way Natural disasters are all around
Recovering from Disaster, the easy way Read More »
Human Error: The Biggest Security Flaw Back in 2011, the United
BYOD, But Be Careful Read More »
Private Cloud Benefits The cloud comes with a long list of
The Benefits of a Private Cloud Read More »
Why Network Security Should Be The Focus of Small Businesses Many
Why Network Security Should Be The Focus of Small Businesses Read More »
Transitioning to Managed IT Services It is difficult for many small
2 major benefits of managed services for small businesses Read More »
Cloud Services Versus a New Server: Which is Best for Your
Cloud Services Versus a New Server: Which is Best for Your Business? Read More »
Your Business Can Benefit from remote Network Monitoring Network downtime and
How Your Business Can Benefit From Remote Network Monitoring Read More »
IT is constantly changing It is difficult for many small businesses
Can managed services increase your productivity? Read More »
The IT Challenge for SMBs Small to medium-sized businesses are no
Network Monitoring and Scale-able Solutions for SMBs Read More »
A New Threat Emerges A new ransomware is making the rounds
Ransomware Changes Your BYOD Phone’s Pin Read More »
Change Management For The IT Documentation Adaptive Challenge Why Change Management
Change Management For The IT Documentation Adaptive Challenge Read More »
Virtual Infrastructure, making IT EASY Let’s say you operate a business
Virtual Infrastructure, making IT EASY Read More »
Advantages of Outsourcing Business IT Consulting The top line item in
Advantages of Outsourcing Business IT Consulting Read More »
Outsourcing IT IT workforce management is in the job description of your
Outsourcing IT Workforce Management Read More »
The Internet of Things Is Growing Rapidly The Internet of Things,
Network Security and The Internet of Things: The FBI Issues a Warning Read More »
Cybersecurity for Nonprofits: Protecting Donor Data in a Digital Age Though
Do Charleston NonProfits Have Enough Network Security? Read More »
Virtual Infrastructure is Good for Your Business If you operate a
Why Virtual Infrastructure is Good for Your Business Read More »
BYOD: A Strategic Advantage When Done Right BYOD can be a
BYOD Pros and Cons Read More »
The Top Ten List of Managed Services David Letterman made the
The Top Ten List of Managed Services Read More »
Your Small Business Need Cloud Services? Cloud services have become essential
Does Your Small Business Need Cloud Services? Read More »
Why Small Businesses Overlook BYOD Risks Many small businesses are unaware
BYOD Security Issues: What to Look Out For Read More »
What Is BYOD and Why It Matters Bring Your Own Device
BYOD done right isn't easy Read More »
Advantages of VoIp Phone Systems If you’re a business owner, then
The Advantages of VoIP Phone Systems Read More »
Why Network Security Matters in Business In business, success often comes
What can Network Security really do for you? Read More »
The Manufacturing Industry and Technology Go Hand in Hand, Why Proper
Understanding the Cloud: What It Really Means We often hear that
Make Money not Rain with Cloud Services Read More »
Disaster Recovery Basics Disaster recovery is something that every business should put
Disaster Recovery Basics Read More »
WHAT MAKES A DISASTER RECOVERY PLAN COMPLETE? The biggest problem with
What Makes a Disaster Recovery Plan Complete? Read More »
Making Smart Tech Choices for Business Growth Business owners are constantly
Tips on Choosing a Cloud Services Provider. Read More »
How to choose the right Cloud Services Business owners trying decide
Inc Magazine's Overview on How to Choose the Right Cloud Services. Read More »
The Data Growth Challenge The growth rate of data among SMBs
Consider IT Consulting to Help Determine How to Handle and Store 'Big Data.' Read More »
Cost-Effective Communication with VoIP Phone Systems VoIP phone systems are the
VoIP Phone Systems Save You Money and Hassle Read More »
How to Migrate To Cloud Services As your business continues to
TBR research: 74% plan to seek help in how to migrate to cloud services Read More »
Is Your IT Change Management Plan Working? Metrics That Matter When
How Can You Measure the Success of Your IT Change Management Plan? Read More »
Why the Anthem Hack Should Be a Wake-Up Call for Senior
Anthem Data Breach Highlights The Importance Of IT Security Services Read More »

Work on the Go: Convenience Meets Risk With laptop computers and
BYOD on the Road: The Risks of Traveling with Your Computing Device Read More »
Understanding and Addressing Unauthorized IT Activities to Strengthen Data Protection When
IT Security Services Question: Does Your Company Have a Shadow IT Problem? Read More »
The Rise of VoIP: A Technology Ahead of Its Time VoIP
VoIP Phone Systems: The Technology Of The Future? Read More »

4 Essential Qualities to Look for in a Managed IT Services
IT Support for Manufacturing Companies: Four Necessary Qualities Read More »

Why Businesses Are Turning to VoIP Phone Systems In today’s fast-paced
3 benefits of VoIP phone systems Read More »
Why Cloud Services Are a Smart Move for Business Productivity Business
How Cloud Services Impact Businesses Read More »
Disaster Recovery Plans: Lessons from Bacardi To increase the odds that
Disaster Recovery Plans: Lessons from Bacardi Read More »
Two Major Problems with BYOD: Security and Expenses Overall, there’s been
Watch Out for Increasing Expenses with BYOD Read More »
You never know when you’ll be the victim of a cyber-attack.
Preparing for an Inevitable Cyber-Attack with Strong Network Security Read More »
What Could Go Wrong Without a Strong IT Change Management Plan?
What Could Go Wrong If You Don’t Have a Strong IT Change Management Plan? Read More »
Myths About VoIP You may have heard a lot about VoIP
4 Common Misconceptions About VoIP Phone Systems Read More »
Unpacking BYOD: The Top 5 Security Risks of Personal Devices at
5 Critical BYOD Risks Read More »

Three Reasons to Love Cloud Services Love is a many-splendored thing.
Three Reasons to Love Cloud Services Read More »

Why Managed IT Services Are a Smart Investment for Businesses Many
Four Reasons You Should Sign Up for Managed Services Today Read More »
Understanding Disaster Recovery: Why Balance Matters We would all like to
How Much Should You Invest in Disaster Recovery? Read More »
5 myths about BYOD Let’s take a moment and dispel some
The Five Myths About BYOD Read More »
The Internet is Always On – But You’re Not The Internet
Who’s Minding IT After the Lights Are Out? Read More »
Disaster Recovery: Plan to Keep Your Business Up and Running Some
Disaster Recovery: Plan to Keep Your Business Up and Running Read More »

Don’t Let a HIPAA Audit Shut You Down: Security Best Practices
How can a HIPAA security audit help my company? Read More »
The Overlooked Threat: Physical Security in a Digital World Barely a
Is Physical Security Still Important in a Digital World? Read More »
The Challenge of Maintaining IT Services Maintaining IT services in an
What Is a Managed Service Provider and What Services Do They Provide? Read More »
Lunch & Learn: Is Your Business Ready for Disaster? Join Us
Charleston Disaster Preparedness Lunch and Learn Series Read More »
Top 10 Keyboard Shortcuts to Boost Productivity Using keyboard shortcuts can
Top Ten Keyboard Shortcuts Read More »

Cloud Confusion: Too Many Options, Too Many Prices Well, you have
Affordable Cloud Service for Your Small Business Read More »
Why the HP TouchPad Failed—and Why We’ve Moved On HP’s TouchPad
The Fall of the HP TouchPad Read More »
Reflecting on Hurricane Irene Irene is well on her way, and
Aftermath, After Thought of 14 Days Read More »

7 Smart Habits to Keep Your Work Computer Secure and Productive
Seven Tips to Help Maintain Your Work Computer Read More »
Are you arriving on-time? Arriving on time is important for all
Are you arriving on-time? Read More »
Amazon Cloud Player: A First Look at Cloud Music Amazon introduced
Amazon Cloud VS Google Music VS iCloud Read More »
Dust kills We all enjoy a clean, safe, and healthy home
Do you Care For Your Tech Like You Do Your Home Read More »
Sony’s PSN Dodges a Hack, But Not a Major Oversight This
PSN logins exploited again, Sony takes pages offline Read More »
Window Management Tips for Single-Screen Users on Windows 11 If you
Switch to Side by Side for your Desktop Read More »
How to Secure Your Facebook Browsing with HTTPS If you use
HTTPS for Facebook Read More »
The Xbox Chronicles: A Silver Lining in the Cloud Not Just
The Xbox and My Son Read More »
What will they come up with Next? The Consumer Electronics Show
CES 2011: What will they come up with next? Read More »
The Reality of IT Budgets in Tough Times In today’s economic
Small business cost savings with PEER to PEER Networking Read More »
Introduction to Antivirus Challenges in Winston-Salem and Charleston Kotori Technologies, LLC,
Rogue Antivirus Product Wars Read More »
Should I Let The Family Computer Whiz Fix My Computer? The
Should I Let The Family Computer Whiz Fix My Computer? Read More »
What Is BlueStacks? BlueStacks is an application that you install on
BlueStacks – Android on Your PC Read More »

Computer Tips: How to Make Your Cursor Easier to See If
Where’s My Cursor? Read More »
Quick Five I’ve seen a lot of computer tips that others
Quick Tech Tips That Make a Big Difference Read More »